OT Security: When Cyber Incidents Become Physical Problems
Operational Technology (OT) security focuses on protecting physical processes, not just data. This post explains what OT security really is, how it compares to IT, and why getting it wrong has real-world consequences.
Daniel Yagüe
1/26/20264 min read
Operational Technology (OT) security refers to the protection of the hardware and software systems used to monitor, control, and manage physical devices, processes, and infrastructure. These systems form the backbone of industrial and critical infrastructure environments.
OT systems are essential for the safe and reliable operation of sectors such as energy, water supply, transportation, and manufacturing. Unlike purely digital environments, failures in OT do not just result in data loss or service disruption. They can lead to physical damage, safety incidents, and environmental impact.
That alone already explains why OT security cannot be treated the same way as traditional IT security.
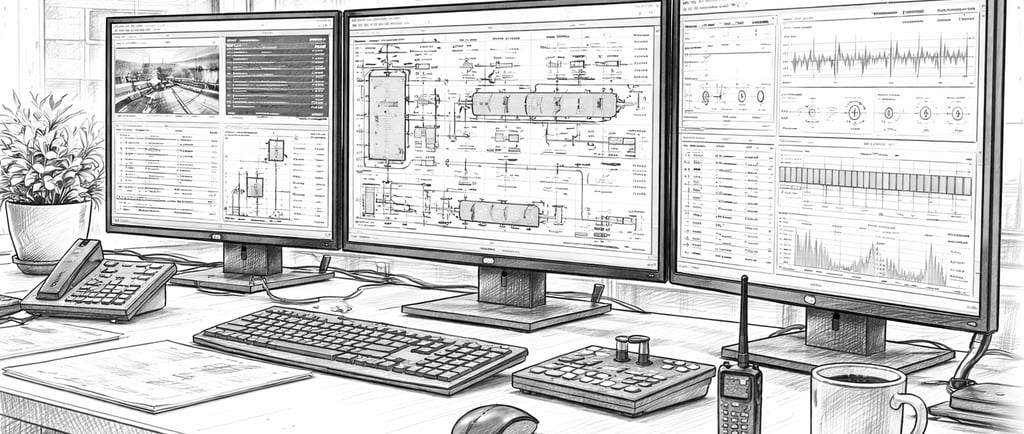
An OT environment is made up of several components, each playing a specific role in controlling physical processes.
One of the most visible components is SCADA (Supervisory Control and Data Acquisition). SCADA systems are used to monitor and control industrial processes, providing real-time data visualization and control capabilities to operators.
Another key element is the PLC (Programmable Logic Controller). PLCs are hardware devices used to automate and control machinery and industrial processes. They execute logic based on inputs from sensors and drive actuators in real time.
Modern OT environments also increasingly include Industrial IoT (IIoT) components. These are connected sensors, devices, and machines that collect data from physical assets and send it to centralized platforms for analysis, optimization, and decision-making. IIoT is often integrated with OT systems to improve efficiency and enable predictive maintenance.
Finally, there are instrumentation and control devices such as sensors, actuators, flow meters, pressure gauges, and temperature sensors. These devices provide the real-time data that controllers use to manage physical processes.
OT and IT: Why the Distinction Matters
OT is often discussed alongside IT, but their focus and constraints are not the same.
While IT systems are built to manage data, applications, and business processes, OT systems exist to control physical processes and machinery. OT environments rely on specialized hardware and software designed for real-time monitoring and control, whereas IT environments usually rely on general-purpose servers, operating systems, databases, and network equipment.
The nature of the data also changes. OT systems handle analog and digital signals related to physical parameters such as temperature, pressure, or flow rates. IT systems work primarily with digital information, often stored and analyzed long after it is created.
Timing is another key aspect. OT systems depend on real-time behavior. Delays can directly affect operations or safety. In IT environments, delays are usually inconvenient, but rarely dangerous.
From a security point of view, priorities also shift. OT security is strongly tied to physical safety and process integrity. A cyber incident can have immediate and tangible consequences. In IT environments, security is primarily centered on data confidentiality, integrity, and availability.
Why OT Is So Important for Industry
OT systems enable industries to optimize physical processes, improve productivity, and reduce downtime. Real-time monitoring and control allow faster adjustments and better use of resources.
OT is also a key enabler for predictive maintenance. By continuously monitoring equipment health and performance, organizations can plan maintenance activities when they are actually needed, reducing unplanned outages and costs.
Automation and optimization driven by OT systems contribute directly to cost reduction, through lower energy consumption, reduced waste, and fewer manual interventions.
Safety is another critical aspect. OT systems automate dangerous tasks, provide real-time safety monitoring, and help ensure compliance with safety regulations. This is especially important in sectors such as manufacturing, chemicals, and mining.
Security Challenges in OT Environments
OT environments face security challenges that are shaped by their operational constraints.
Many OT systems rely on legacy equipment with long lifecycles. These systems often lack modern security features, and upgrading or replacing them can be complex and expensive.
As OT systems become more connected to IT networks and cloud platforms, the attack surface expands. Without careful design, this increased connectivity introduces new vulnerabilities.
Another major challenge is the lack of regular security updates. OT devices are often deployed for decades, and vendors may not provide frequent patches. This leaves systems exposed to known vulnerabilities for long periods of time.
There is also often limited security awareness in OT contexts. Security practices that are obvious in IT—such as encrypting exposed services or protecting internet-facing systems—are not always applied when physical devices or actuators are connected to external platforms.
Common Threats Against OT Systems
OT environments are exposed to a wide range of threats, many of which can have serious consequences. These include:
Malware and ransomware, disrupting control processes or rendering systems unusable
Zero-day exploits, targeting unknown vulnerabilities
Denial-of-service attacks, affecting system availability
Insider threats, involving misuse of authorized access
Supply chain attacks, introducing compromised hardware or software during procurement
These threats target not just information, but the physical processes that OT systems control.
Real-World OT Attacks
Several well-known incidents highlight the impact of OT security failures.
In 2010, the Stuxnet attack targeted SCADA systems used in Iran’s nuclear facilities. The malware manipulated centrifuge speeds, causing physical damage while hiding its actions from operators. This incident demonstrated that cyber operations could directly damage industrial equipment.
In 2021, the Ukraine power grid was attacked, leading to power outages affecting hundreds of thousands of people. Attackers remotely accessed and manipulated control systems in power distribution substations.
That same year, the Oldsmar water treatment plant in Florida was compromised. An attacker gained remote access to the control system and attempted to increase sodium hydroxide levels in the water supply. Operators detected the activity in time, preventing harm to the public.
Wrapping up: why OT security needs its own approach
OT security is not just IT security applied to industrial systems. It is about protecting physical processes, human safety, and critical infrastructure.
Understanding how OT environments work, how they are structured, and how risks manifest in the physical world is essential. Without that understanding, security controls may look solid on paper while failing where it matters most: in real operations.
