“Should Your Organization Pursue IEC 62443-4-1 or 4-2 Certification? A Business-Driven Decision Framework
Before pursuing IEC 62443-4-1 or 4-2 certification, organizations must align cybersecurity with business drivers. In this article we will explore how to build traceability, define measurable objectives, and decide when certification delivers real strategic value.
IEC 62443
Daniel Yagüe
2/5/20266 min read
Introduction — The Certification Trap
In recent years, the IEC 62443 series has become widely recognized as one of the most respected frameworks for securing industrial automation and control systems. In particular, certifications aligned with IEC 62443-4-1 and IEC 62443-4-2 are increasingly viewed as indicators of strong cybersecurity maturity in industrial product development and component security.
As awareness of industrial cybersecurity risks continues to grow, many organizations are asking an important question:
Should we pursue IEC 62443 certification?
The reason behind I decided to write this article is, because in practice, this question is often answered too quickly and for the wrong reasons. Certification initiatives are frequently driven by industry trends, competitor positioning, or internal technical enthusiasm. While these motivations are understandable, they can lead organizations into complex certification programs without fully understanding whether certification truly supports their strategic business objectives.
Pursuing IEC 62443 certification is not simply a technical or compliance decision. It introduces long-term commitments that influence product development processes, supplier management, organizational governance, lifecycle maintenance, and overall security investment strategy. When approached without clear business justification, certification can consume significant resources while delivering limited strategic value.
A more effective approach is to start from the business perspective. Organizations should first identify the business drivers motivating cybersecurity investment and translate those drivers into measurable security attributes that reflect what the business actually needs to protect, achieve, or guarantee. Only then can certification be evaluated as a justified outcome rather than a predefined goal.
This article presents a business-driven decision framework to help organizations determine when pursuing IEC 62443-4-1 and 4-2 certification is aligned with the company strategy, and when alternative security improvement approaches may be more appropriate.
Understanding What IEC 62443-4-1 and 4-2 Actually Represent
Before deciding whether certification should be pursued, it is essential to understand what IEC 62443-4-1 and IEC 62443-4-2 are designed to achieve. While both belong to the same industrial cybersecurity framework, they address different but complementary aspects of product security.
IEC 62443-4-1: Secure Product Development Lifecycle
IEC 62443-4-1 focuses on the processes used to design, develop, maintain, and support industrial automation and control system components. Rather than defining technical security features, this standard establishes requirements for how security is embedded into the entire product lifecycle.
Organizations pursuing certification against this standard must demonstrate structured and repeatable practices across areas such as:
Security requirements definition
Secure design and implementation
Vulnerability management
Security testing and verification
Secure maintenance and update processes
Supply chain security governance
Achieving certification requires organizations to integrate cybersecurity into engineering culture, development methodologies, and governance structures. It impacts not only engineering teams but also product management, supplier relationships, and long-term product support strategies.
IEC 62443-4-2: Technical Security Capabilities of Products
IEC 62443-4-2 focuses on the security capabilities that industrial automation and control system components must provide. While 4-1 addresses how products are built securely, 4-2 defines what security functions products must implement.
These requirements typically include:
Identification and authentication mechanisms
Access control enforcement
System integrity protection
Data confidentiality capabilities
Security event detection and logging
Resistance to malicious or unintended misuse
Certification against 4-2 demonstrates that a product meets defined technical security expectations required by customers and operators integrating components into industrial environments. In practice, achieving IEC 62443-4-2 certification typically requires organizations to demonstrate secure development lifecycle processes aligned with IEC 62443-4-1 or equivalent security governance practices, since product security capabilities are expected to be supported by structured and repeatable development methodologies.
Certification Impact Extends Beyond Security Controls
Certification against either standard extends well beyond implementing individual security features or procedures. Both introduce long-term operational and organizational commitments, including:
Changes to development and engineering workflows
Increased documentation and traceability requirements
Ongoing vulnerability monitoring and patch management
Enhanced supplier and third-party risk management
Continuous improvement and audit readiness
Because of this broad impact, certification decisions should not be approached purely as technical security initiatives. They influence how organizations design products, manage risk, allocate resources, and position themselves in the market.
Understanding this scope is critical before determining whether certification aligns with business priorities — which is why the decision should begin with identifying business drivers.
Why Certification Should Start With Business Drivers
Organizations often begin certification initiatives by evaluating technical maturity, reviewing security gaps, or responding to customer or regulatory pressure. While these are legitimate triggers, they rarely answer the most important question: What business outcome is the certification expected to support?
When certification is pursued without a clearly defined business motivation, organizations may treat it as a compliance exercise rather than a strategic capability.
A business-driven approach starts by identifying the drivers that justify cybersecurity investment. These drivers typically originate from market expectations, operational needs, regulatory environments, or competitive positioning.
Common drivers influencing certification decisions include:
Strengthening customer trust and market credibility
Meeting procurement or supply chain security requirements
Supporting entry into regulated or critical infrastructure markets
Reducing product liability and operational risk exposure
Differentiating products in competitive industrial sectors
Supporting long product lifecycle commitments
While these drivers provide direction, they are often too broad to guide concrete certification decisions. Organizations must translate them into measurable security priorities defining what must be protected or guaranteed.
Without this this step, certification can become an end goal rather than a solution to a specific business problem.
Translating Business Drivers Into Business Attributes
Following SABSA framework, we find that business drivers define why security matters and business attributes define how security must perform to support those goals.
Business attributes make security expectations explicit by defining what must be protected. They transform strategic intent into practical decision criteria and create traceability between business priorities and certification strategies.
Typical attributes relevant to industrial product security include:
Integrity – Protection against unauthorized modification
Availability – Operational resilience across product lifecycles
Confidentiality – Protection of sensitive operational and intellectual property data
Trust and Assurance – Demonstrable secure development and governance
Accountability and Traceability – Monitoring, auditing, and forensic investigation capability
Maintainability and Resilience – Secure updates and lifecycle sustainability
Compliance and Governance – Regulatory and contractual alignment
By defining and prioritizing these attributes, organizations establish measurable targets guiding certification decisions.
Building Traceability and Measurable Justification for Certification
Once business attributes are defined, organizations can build traceability between business objectives, security requirements, and certification outcomes. However, traceability alone is insufficient. Organizations must also define measurable objectives demonstrating that certification delivers tangible improvements.
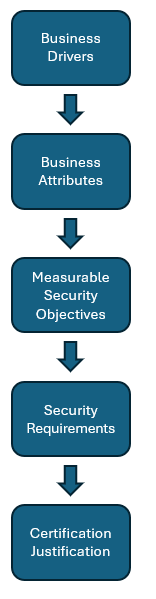
Structured Decision Path
Translating Attributes Into Measurable Objectives
Each business attribute should be supported by measurable performance indicators that allow organizations to evaluate whether security initiatives — including certification — are delivering expected business outcomes.
Once measurable objectives are defined, organizations can evaluate how IEC 62443-4-1 and 4-2 certification contributes to achieving them.
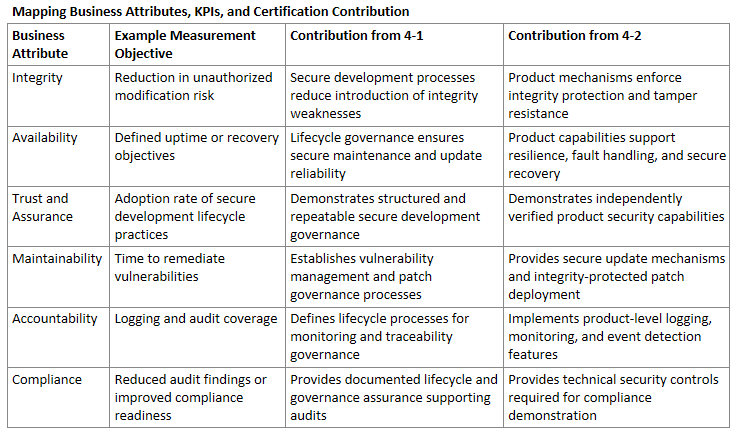
Let´s see an example with the attributes we previously defined:
IEC 62443-4-1 primarily contributes to measurable improvements related to development governance, lifecycle assurance, and organizational security maturity. It reduces the likelihood that vulnerabilities are introduced during product development and improves the organization’s ability to maintain security throughout the product lifecycle.
IEC 62443-4-2 primarily contributes to measurable improvements in technical product protection. It ensures components implement security mechanisms that protect operational environments and resist cybersecurity threats during deployment and operation.
Together, these certifications provide complementary assurance: 4-1 addresses how products are developed and maintained securely, while 4-2 validates the security capabilities embedded within the products themselves.
By linking business attributes, measurable KPIs, and certification contributions, organizations can evaluate certification decisions using objective performance criteria rather than industry momentum alone. This approach allows decision makers to determine whether certification investments directly improve measurable security and business outcomes.
It also enables organizations to continuously evaluate certification value over time by monitoring whether targeted performance indicators improve following certification adoption.
Once organizations establish traceability between business drivers, measurable attributes, and certification outcomes, the next step is applying this decision framework to real-world scenarios.
In practice, certain business environments consistently demonstrate strong alignment between measurable security objectives and the value delivered by IEC 62443 certification. Understanding these scenarios helps organizations determine when certification is likely to provide strategic and operational benefits.
When IEC 62443 Certification Clearly Makes Sense
Certification frequently provides strong value in scenarios where cybersecurity assurance directly affects market access, trust, regulatory positioning, or lifecycle sustainability. For example:
Industrial Product Manufacturers Supporting Critical Infrastructure: Certification strengthens procurement credibility, regulatory acceptance, and assurance in safety-sensitive sectors.
Vendors Facing Increasing Supply Chain Security Requirements: Certification provides independent validation and reduces repeated customer security assessments.
Organizations Supporting Long Product Lifecycles: Certification supports structured vulnerability management and secure update mechanisms across extended product lifetimes.
Companies Using Security as Market Differentiation: Certification can enhance brand credibility and competitive positioning.
Organizations Preparing for Future Regulatory Requirements: Proactive certification reduces long-term compliance disruption.
Companies Planning a Multi-Product Portfolio Strategy: When multiple products are expected to be developed and launched over time, certification becomes a scalable capability rather than a one-time cost. Governance structures, secure development practices, and audit readiness can be reused across product lines, significantly improving return on investment.
When Certification Might Not Be the Right Priority
Low-Risk or Non-Critical Components: Internal security programs may provide sufficient protection without full certification.
Internal-Only Solutions: External assurance may provide limited business value.
Early-Stage Product Development: Foundational security capabilities should typically precede certification.
Resource-Constrained Organizations: Certification investments must be evaluated against alternative security improvements.
Markets With Limited Regulatory or Customer Demand: Organizations may monitor trends while strengthening internal maturity.
Conclusion — Certification as a Business Decision, Not a Security Trend
IEC 62443 certification provides powerful cybersecurity assurance but should not be pursued solely as an industry benchmark. Certification introduces long-term commitments influencing development, supply chain governance, and lifecycle management.
Organizations achieve stronger outcomes when certification decisions originate from business drivers and measurable attributes. This ensures certification supports business resilience, product trust, and operational sustainability.
For organizations where certification is strategically justified, the next challenge is understanding the required investment.
In the next article, we will analyze the cost factors involved in implementing IEC 62443-4-1 and 4-2 and provide practical guidance for estimating certification investment and planning implementation strategies.